Prevent This: Supply Chain Software Attacks
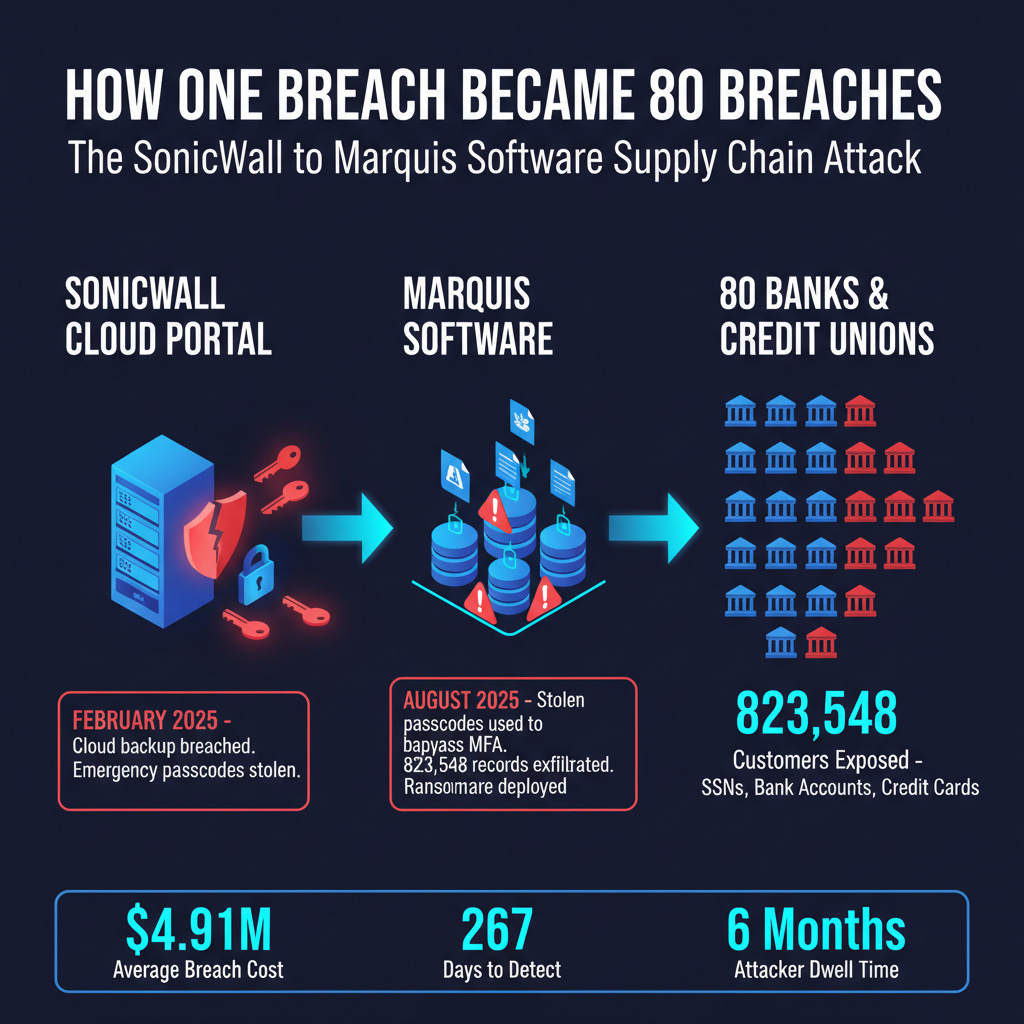
One compromised vendor. 823,548 bank customers exposed. Zero shots fired.
What Happened?
Picture your building’s security company storing a copy of every tenant’s master key in a warehouse. A thief breaks into the warehouse, copies the keys, then robs 80 apartments. The tenants’ locks were fine. The security company’s warehouse was the weak link.
That is almost exactly what happened to Marquis Software Solutions.
According to Marquis’ lawsuit against SonicWall, In February 2025, attackers compromised SonicWall’s cloud portal and stole firewall configuration data, including emergency backup passcodes, for a subset of customers. Those passcodes were designed to bypass normal authentication in emergencies. The attackers sat on the stolen keys for months.
Then, in August 2025, they used those passcodes to walk straight into Marquis Software’s network. Marquis provides core banking software to community banks and credit unions across the country. Once inside, the attackers exfiltrated Social Security numbers, bank account details, and credit card numbers belonging to 823,548 people across 80 banks and credit unions, then deployed ransomware.
No bank was directly attacked. Every bank was affected.
This is a double supply chain attack: SonicWall (the firewall vendor) fell first, which enabled the breach of Marquis (the banking software vendor), which exposed data from 80+ financial institutions and their customers. Two links in the chain, hundreds of thousands of victims.
And Marquis was not alone. In March 2026:
APT41 (a Chinese state-backed group) was revealed to have been inside F5 Networks for over 12 months, potentially deploying backdoors on customer systems. F5 makes the access control software that banks, hospitals, and government agencies depend on.
The Trivy vulnerability scanner (covered last week), a security tool used by thousands of enterprises, was itself compromised when attackers poisoned 76 of 77 release tags on GitHub. The tool organizations trusted to find vulnerabilities became the vulnerability.
The GlassWorm campaign planted malicious code in 433 packages, repositories, and IDE extensions across GitHub, npm, and VSCode marketplaces, hiding payloads in invisible Unicode characters.
The good news is that there are steps that you can take to minimize the risk from your supply chain…. Like insisting on a Software Bill of Materials (SBOM) among other controls.
Why Should You Care?
Supply chain attacks are growing faster than almost any other category:
30% of all data breaches in 2025 involved a third-party vendor, double the rate from previous years (DeepStrike)
Supply chain breaches cost $4.91 million on average and take the longest to detect, averaging 267 days from compromise to containment (IBM Cost of a Data Breach Report, 2025)
877,522 malicious packages were detected in open-source software repositories in 2025, a 73% increase over 2024 (ReversingLabs/Sonatype)
$60 billion in global losses from software supply chain attacks in 2025, projected to reach $138 billion by 2031 (Cybersecurity Ventures)
Here is the part that makes supply chain attacks different from every other type: you can do everything right and still get hit. Your firewalls are configured correctly. Your employees passed phishing training. Your systems are patched. But if your software vendor, or your vendor’s vendor, gets compromised, the attackers ride in on trusted software through the front door.
How Does This Work?
Think of it like a contaminated ingredient in a food supply. The restaurant did nothing wrong. The ingredient passed inspection. But everyone who eats the meal gets sick.
Software supply chains work the same way. Modern organizations depend on dozens (sometimes hundreds) of vendors, each of which depends on their own set of vendors, open-source libraries, cloud providers, and service partners. An attacker who compromises one link anywhere in that chain can reach every organization downstream.
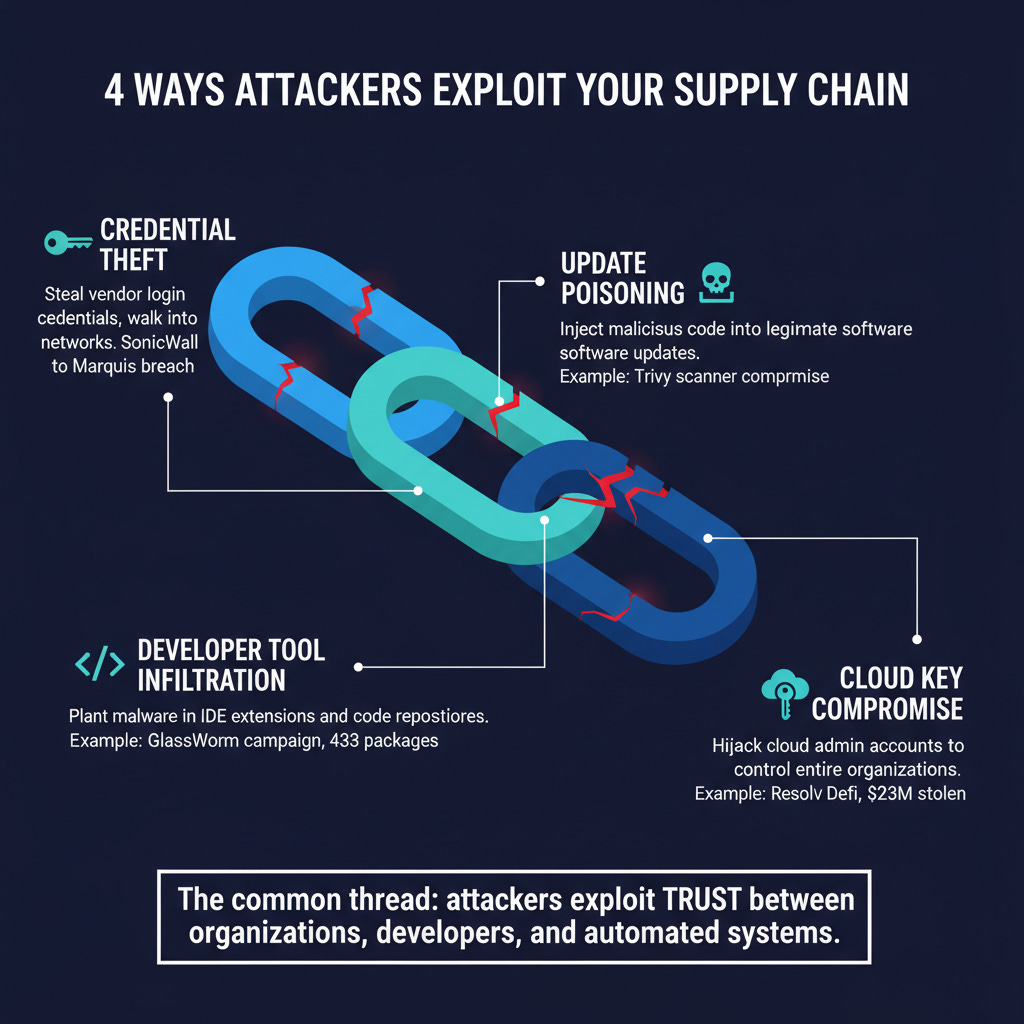
The most common supply chain attack patterns right now:
Vendor credential theft (the Marquis pattern): Steal login credentials or backup codes from a vendor’s systems, then use that access to reach their customers. The attackers never need to touch the target directly.
Software update poisoning (the Trivy pattern): Inject malicious code into a legitimate software update or open-source package. Every organization that installs the update gets compromised automatically.
Developer environment infiltration (the GlassWorm pattern): Plant malicious code in developer tools, IDE extensions, or code repositories. When developers use these tools, the malicious code harvests credentials and tokens that open doors to production systems.
Cloud infrastructure compromise (the Resolv DeFi pattern): Target the cloud management layer, such as AWS key management or Microsoft Intune admin accounts, rather than the application itself. One privileged cloud key can unlock an entire organization.
What makes these attacks so effective is trust. Organizations trust their vendors. Developers trust their tools. Automated systems trust signed updates. Attackers exploit that trust.
What Can You Do?
If You Run an Organization
1. Know your ingredient list.
You cannot protect what you do not know about. Build and maintain a Software Bill of Materials (SBOM), an inventory of every piece of software and every vendor your organization depends on. Our colleagues at NetRise have built an excellent platform for exactly this: their tools generate SBOMs from binaries, firmware, and containers, then map every component back to known vulnerabilities and, with their new Provenance feature (launched March 2026), trace which developers and organizations are behind each open-source component. If the Trivy compromise taught us anything, knowing what is inside your software stack is no longer optional.
2. Verify your vendors’ vendors.
Third-party risk assessments should not stop at your direct vendors. Ask them: who are your critical vendors? How do you secure their access? According to Marquis, the Marquis breach happened because SonicWall’s cloud backup practices were inadequate. Marquis trusted SonicWall. Eighty banks trusted Marquis. The chain broke at the link nobody was watching.
3. Lock down admin accounts like they are the crown jewels.
Phishing-resistant multi-factor authentication (hardware keys, not SMS codes) on every administrative account. No exceptions. The Stryker wiper attack (200,000 devices destroyed in March 2026) started with a single compromised Microsoft Intune admin account.
4. Segment your network so one breach cannot reach everything.
If a vendor is compromised, limit what they can access. Your banking software vendor does not need access to your HR systems. Your HVAC vendor does not need access to your customer database.
5. Plan for your vendor getting breached.
Have an incident response plan that specifically addresses the scenario where a trusted vendor is compromised. Know which data is at risk, how to isolate affected systems, and who to call. Practice it.
If You Are a Professional (Any Field)
1. Use a password manager and unique passwords everywhere.
If one service is breached, reused passwords give attackers access to your other accounts. A password manager makes unique passwords easy.
2. Turn on multi-factor authentication, and secure the backup codes.
MFA is essential, but in the Marquis case, attackers bypassed it using stolen emergency backup passcodes. Store your backup codes in a secure location (a password manager or a physical safe), not in a cloud document.
3. Be cautious with browser extensions and software add-ons.
The GlassWorm campaign hid malicious code inside 72 fake VSCode extensions that mimicked popular developer tools. The same approach works with browser extensions, mobile apps, and plugins of all kinds. Stick to well-known, well-reviewed tools, and remove anything you are not actively using.
4. Update deliberately, not blindly.
Patching remains critical, but after the Trivy compromise, security experts recommend a brief waiting period (24 to 48 hours) before adopting updates from sources that are not critical security patches. This gives the community time to catch poisoned updates before they spread.
The Bottom Line
The biggest cybersecurity risk to your organization may not be your own security. It may be your vendor’s. Supply chain attacks exploit the trust between organizations, and they are growing in frequency, sophistication, and impact. You cannot eliminate the risk, but you can reduce your exposure by knowing your software ingredients, verifying your vendors, and planning for the day one of them gets compromised.
Research Sources:
Intruvent CTI Cloud
American Banker, “Marquis Breach Toll Rises to 80 Banks, 824,000 Consumers”
TechCrunch, “Marquis Sues SonicWall Over Ransomware Breach”
IBM, 2025 Cost of a Data Breach Report
DeepStrike, “Supply Chain Attack Statistics 2025”
Cybersecurity Ventures, “Software Supply Chain Attack Costs”
Microsoft Security Blog, “Trivy Supply Chain Compromise Guidance”
Intruvent Technologies, BRACE Threat Intelligence Reports, March 2026
Last Updated: March 31, 2026




Very solid and great research. Love Oreo and Bean's take on this one!