Intruvent EDGE: The Russian Cyber Toolkit Evolves
From Poland's Power Grid to a $300K Zero-Day Marketplace
On December 29, 2025, while most of the world was preparing for New Year’s celebrations, Russian military hackers launched what Polish officials are calling the largest cyberattack in the country’s history.
They went after Poland’s power grid. And they did it exactly ten years to the day after Sandworm’s historic attack on Ukraine’s grid, the first malware-facilitated blackout in history.
That anniversary timing wasn’t coincidental.
Meanwhile, five Russian APT groups have been weaponizing a single vulnerability, CVE-2025-8088 in WinRAR, in what looks like a coordinated shopping spree at an underground exploit marketplace. One seller. Multiple state-sponsored buyers. $80,000 per exploit.
This is how Russian offensive operations are evolving.
Editor’s Note: If you’re in critical infrastructure, grab ourThreat Hunting Guides (THGs) for Volt Typhoon and Sandworm. Send them to your colleagues. The Power Grid targeting in Poland is a preview of what’s coming to more places. Let’s get ahead of it.
Part 1: The Poland Power Grid Attack
What Happened
The attacks hit on December 29-30, 2025, targeting approximately 30 distributed energy resources (DERs): wind farms, solar installations, and combined heat-and-power plants. The attackers deployed a new wiper that ESET has named DynoWiper.
Poland’s cyber defenders stopped it. No blackouts. No service disruptions. But ESET researchers who analyzed the malware say the attackers knew exactly what they were doing.
If successful, this attack could have left 500,000 Polish citizens without heat during winter.
Why This Matters for Defenders
This attack represents a shift in targeting strategy. Previous ICS/OT attacks hit centralized infrastructure: big power stations, transmission substations. DynoWiper went after distributed resources.
Wind farms and solar installations often have less security investment than traditional power plants. They’re managed by smaller operators. They’re geographically dispersed. And there are a lot of them.
Dragos researchers confirmed that the attackers demonstrated deep knowledge of RTU (Remote Terminal Unit) deployment patterns. They weren’t just throwing malware at the problem. They’d done their homework.
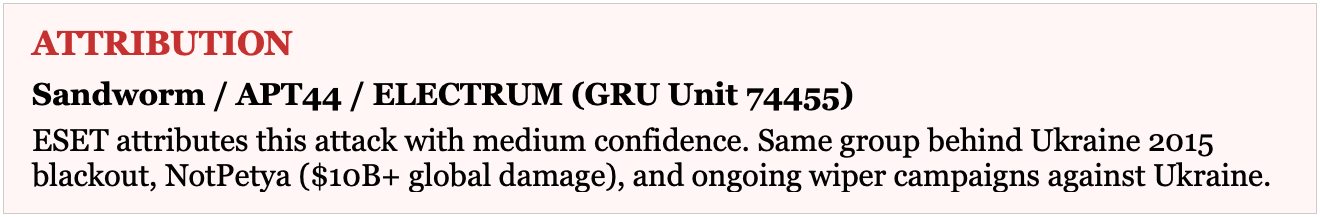
ATTRIBUTION
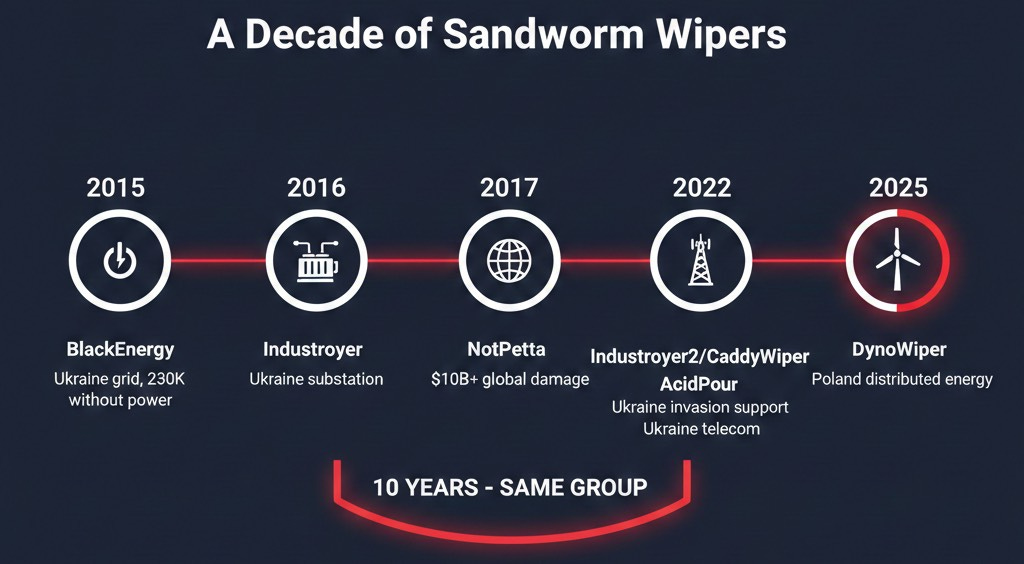
The Wiper Timeline
Sandworm has been refining destructive malware for a decade. The pattern is clear:
This marks the first known Sandworm attack targeting a NATO member’s critical infrastructure. That’s not a small detail.
Part 2: The WinRAR Weaponization
Five APT Groups, One Vulnerability
CVE-2025-8088 is a path traversal vulnerability in WinRAR that allows attackers to write malicious files to arbitrary locations on a victim’s system. CVSS 8.8. Patched in version 7.13 on July 30, 2025.
Here’s the problem: first exploitation was detected on July 18, 2025, twelve days before the patch. Someone was using this as a zero-day.
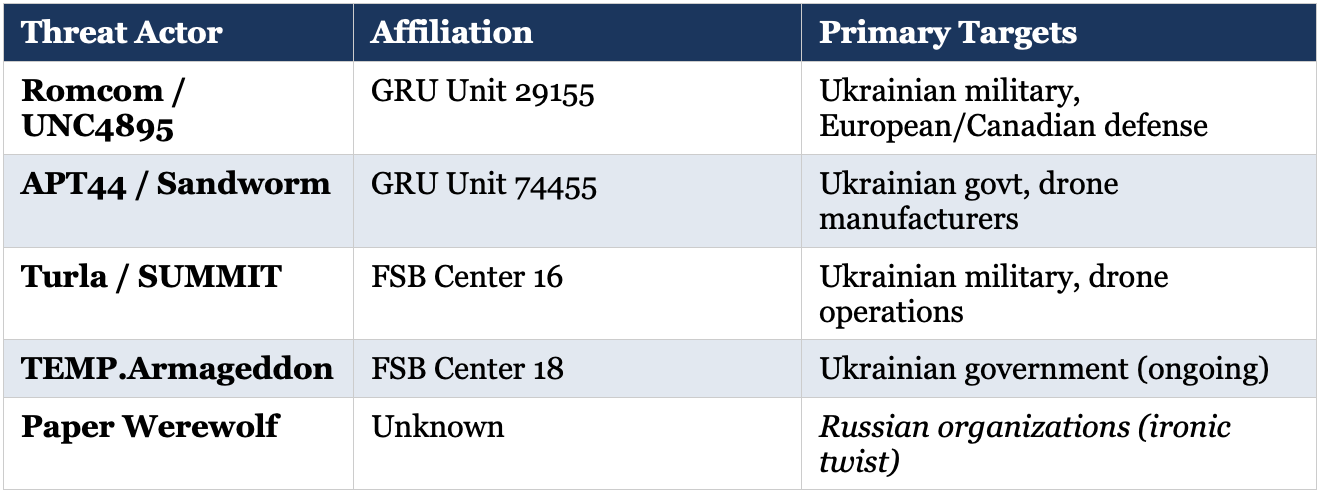
ESET and BI.ZONE researchers have now documented five distinct Russian APT groups exploiting this vulnerability:
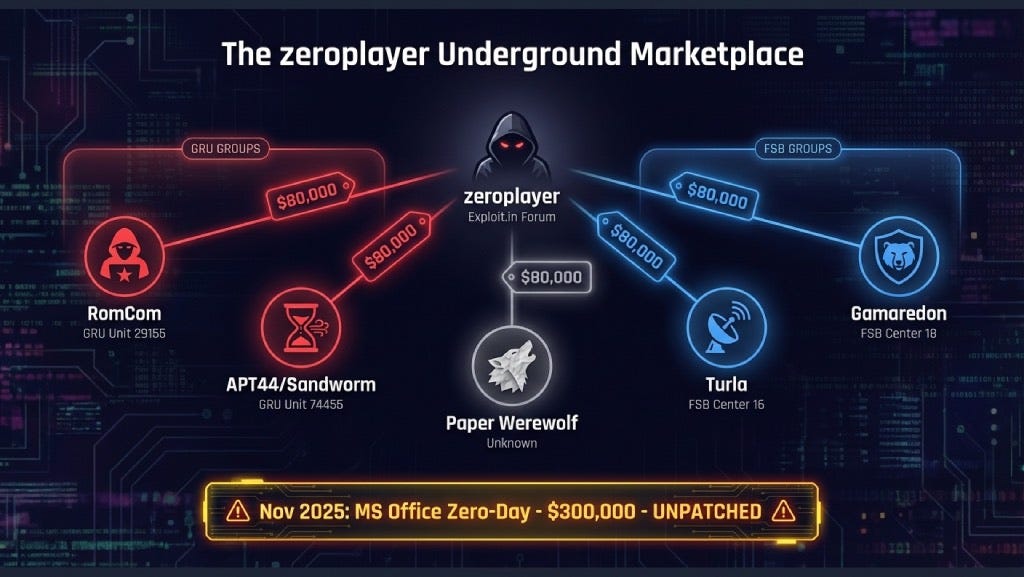
So how did five different state-sponsored groups all get access to the same zero-day?
The Underground Connection: “zeroplayer”
On July 7, 2025, eleven days before the first detected exploitation, a dark web actor called “zeroplayer” advertised a WinRAR zero-day on the Exploit.in forum. Price: $80,000.
ESET and BI.ZONE researchers confirmed that RomCom and Paper Werewolf likely acquired exploits from the same source. One seller, multiple nation-state buyers.
zeroplayer’s portfolio since July 2025:
• July 2025: WinRAR RCE (CVE-2025-8088) - $80,000
• September 2025: Corporate VPN RCE - price unspecified
• October 2025: Windows LPE - $100,000
• November 2025: Microsoft Office sandbox escape + RCE - $300,000
That Microsoft Office zero-day is still unpatched. Someone paid $300,000 for it. Place your bets on who.
Part 3: The Convergence
When you map these operations together, patterns emerge that tell a bigger story about Russian offensive cyber capabilities:
1. Shared Exploit Sourcing
Multiple Russian APTs are buying from the same underground marketplace. This suggests either coordination or simply that good exploits attract all buyers. Either way, when a new zero-day hits the market, expect rapid multi-actor adoption.
2. APT44 Running Parallel Operations
Sandworm wasn’t just deploying DynoWiper against Poland. They were simultaneously running WinRAR-based espionage campaigns against Ukrainian targets. Destructive and espionage operations, same time, same group.
3. FSB Inter-Agency Collaboration
ESET documented Gamaredon (FSB Center 18) providing initial access that Turla (FSB Center 16) later exploited between February and April 2025. Two FSB units, working in sequence. This kind of collaboration was theoretical until researchers caught them doing it.
4. GRU Unit Coordination
Unit 29155 (RomCom) and Unit 74455 (Sandworm) are both GRU. Both running parallel operations against similar target sets. They’re almost certainly coordinating at some level.
5. Unified Targeting
All roads lead to the same targets: Ukrainian military, drone manufacturers, NATO-aligned defense organizations. This convergence is strategic.
What You Should Do About It
This Week:
• Update WinRAR to 7.13+. No, it doesn’t auto-update. Yes, you probably have to push this manually.
• Monitor Windows Startup folders for new .lnk, .hta, .bat files. That’s where the WinRAR exploit drops payloads.
• Block archive extraction that writes outside the target directory.
For Critical Infrastructure/OT:
• Review your OT/ICS network segmentation. Can your RTUs be reached from IT networks?
• Audit remote access to distributed energy resources. If you’re managing wind farms or solar installations remotely, assume someone is interested.
• Implement immutable backups for ICS configuration files. Wipers don’t care about your backup schedule if they can reach your backups.
Detection Priorities:
• DynoWiper: SHA-1 4EC3C90846AF6B79EE1A5188EEFA3FD21F6D4CF6 (Detection: Win32/KillFiles.NMO)
• Monitor for NTFS Alternate Data Stream (ADS) read/write activity. That’s how the WinRAR exploit hides payloads.
• Alert on RAR extraction events writing to %AppData%\Microsoft\Windows\Start Menu\Programs\Startup\
Quick Reference: Key IOCs
DynoWiper (Poland Attack)
• SHA-1: 4EC3C90846AF6B79EE1A5188EEFA3FD21F6D4CF6
• Detection: Win32/KillFiles.NMO
CVE-2025-8088 WinRAR Exploitation
• Vulnerable: WinRAR ≤7.12
• Patched: WinRAR 7.13 (July 30, 2025)
• Exploit mechanism: Path traversal via NTFS Alternate Data Streams
MITRE ATT&CK Techniques
• T1566 - Phishing (spearphishing with weaponized RAR)
• T1204 - User Execution
• T1547.001 - Registry Run Keys / Startup Folder
• T1564.004 - NTFS File Attributes (ADS concealment)
• T1485 - Data Destruction
Sources
• ESET Research - DynoWiper analysis (January 2026)
• ESET Research - CVE-2025-8088 exploitation by Russian APTs
• Google Threat Intelligence Group - RomCom/UNC4895 campaigns
• BI.ZONE - Paper Werewolf activity report
• Dragos - ICS/OT targeting assessment
• CERT-Polska - Poland grid attack confirmation
• Mandiant - Gamaredon-Turla collaboration analysis
• Underground intelligence: Exploit.in forum, RAMP forum
Thanks for reading Intruvent Edge! This post is public so feel free to share it.
Subscribe for free to receive new posts and support our work.
The Intruvent Edge is published bi-weekly. Prevent This is published weekly. Subscribe at intruvent.com/edge
Have questions? Contact the Intruvent team at contact@intruvent.com