INTRUVENT EDGE: January 2026 Threat Trends
The Monthly Intelligence Digest for Security Leaders
Theme of the Month: The Perimeter Has Dissolved
Cross-sector analysis for our January BRACE reports was telling. January’s threat landscape delivered a verdict: the traditional security perimeter is gone. Attackers are targeting things outside the traditional parameter: operating iyour cloud APIs, your SaaS integrations, your OT networks. Often without ever touching your endpoints. You’ll need to move fast to regain the advantage.
The Numbers That Matter
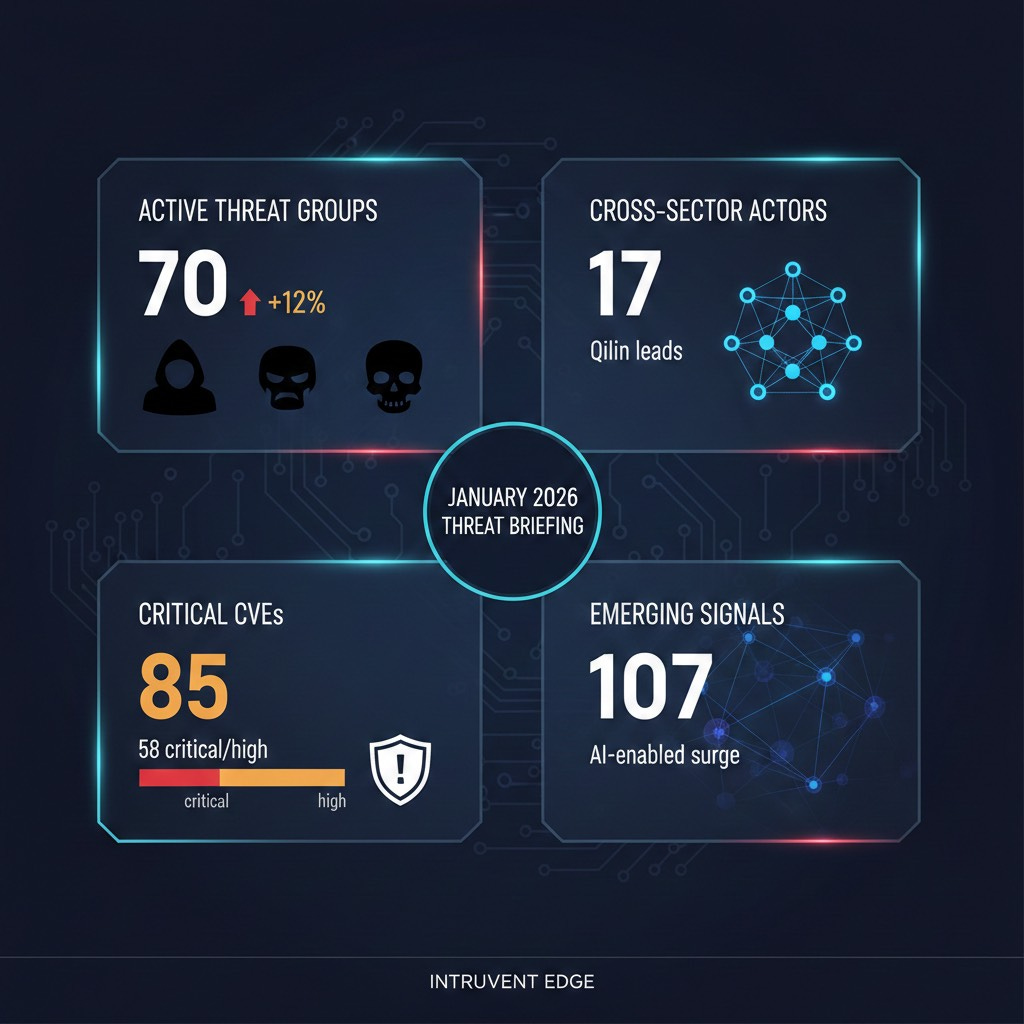
Active Threat Groups: 70 (up 12% month-over-month, highest count since tracking began)
Cross-Sector Actors: 17 (Qilin leading, cartel coordination accelerating)
Critical CVEs: 85 tracked (58 rated CRITICAL or HIGH, exploitation pace exceeds patching)
Emerging Signals: 107 indicators (AI-enabled attacks surging across sectors)
1. Codefinger: Ransomware Without the Malware
The first ransomware that doesn’t need your network.
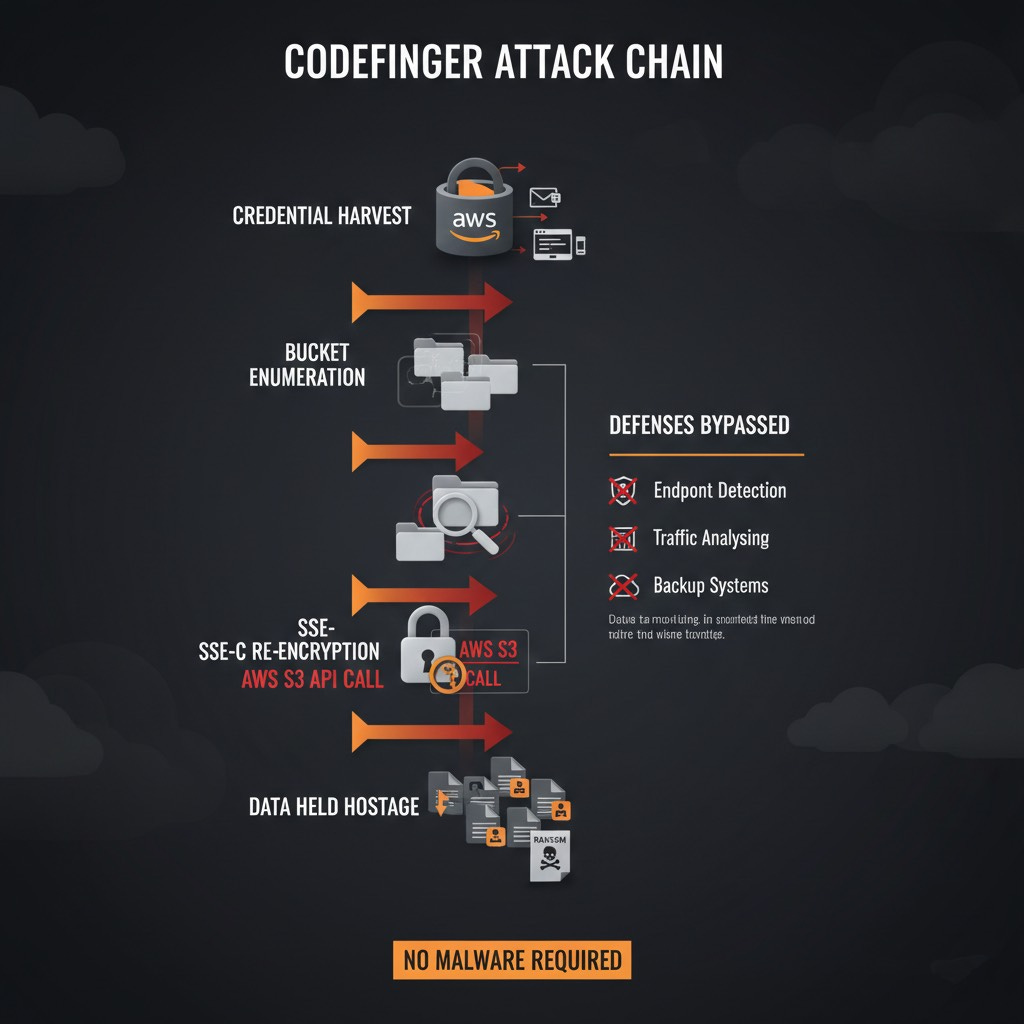
In January, Halcyon’s researchers disclosed “Codefinger,” a ransomware operation weaponizing AWS S3’s Server-Side Encryption with Customer-Provided Keys (SSE-C) to lock organizations out of their own cloud storage. No malware. No lateral movement. No endpoint compromise. Just API calls.
How it works:
Attackers obtain leaked AWS credentials from GitHub commits, phishing, or infostealer logs. They enumerate S3 buckets and identify valuable data. Using the S3 API, they re-encrypt objects with attacker-controlled SSE-C keys. Original data becomes mathematically unrecoverable without the key.
Why your current defenses won’t help: EDR doesn’t see it because there’s no malware. Network monitoring misses it because the traffic is legitimate API calls to AWS. Backup systems can’t help if backups are stored in the same S3 buckets. The attack happens entirely within AWS’s legitimate service layer. CloudTrail logs show the activity, but only if you’re watching.
Defensive priority: Audit IAM permissions for s3:PutObject with SSE-C capabilities. Enable S3 Object Lock for critical data. Deploy CloudTrail alerting for unusual SSE-C operations. Segregate backup storage with separate credentials.
Source: Halcyon Research, January 2026
2. Eight Minutes: When Attackers Move Faster Than Your SOC
From phishing email to full AWS environment compromise in under 10 minutes.
A January incident reconstructed by cloud security researchers at Wiz revealed a new operational tempo: threat actors using AI-assisted tooling achieved complete cloud environment takeover in just 8 minutes.
The attack chain:
0:00: Spear-phishing email with malicious OAuth consent link
0:45: Victim grants OAuth app access to M365 mailbox
2:30: Automated credential harvesting from mailbox attachments
4:00: AWS console login using harvested service account credentials
5:30: Lambda functions enumerated, secrets extracted
8:00: New IAM admin user created, persistence established
Traditional incident response assumes hours or days. Eight minutes doesn’t give SOC teams time to triage an alert, let alone contain a breach.
The takeaway: Speed is the new competitive advantage for attackers. Detection must be automated, and response playbooks need to trigger without human approval for high-confidence signals.
Source: Wiz Cloud Threat Intelligence, January 2026
3. Bybit’s $1.5 Billion Lesson: Lazarus Never Sleeps
The largest single crypto theft in history. Here’s how they did it.
North Korea’s Lazarus Group executed a $1.5 billion heist against cryptocurrency exchange Bybit in January, eclipsing the $620M Ronin Bridge attack as the largest crypto theft ever recorded.
Technical execution:
Social engineering campaign targeting exchange developers. Supply chain compromise of a trading interface component. Hot wallet credentials exfiltrated via memory scraping. Funds dispersed across 50+ wallets within 90 minutes.
The strategic angle: At $1.5B, this single operation likely funds a significant portion of North Korea’s weapons programs for 2026. Lazarus isn’t criminal in the traditional sense. It’s a revenue-generating arm of a sanctions-evading government. The financial services sector remains the highest-value target for state-sponsored actors with economic motivations.
For financial institutions: Third-party code review isn’t optional. Hot wallet architecture must assume compromise. Behavioral analytics on transaction patterns are essential.
Source: Chainalysis, FBI IC3 Advisory, January 2026
4. Sandworm Returns: DynoWiper and Poland’s Grid
Russia’s elite cyber unit tests new destructive capabilities in NATO territory.
January saw Sandworm (GRU Unit 74455) deploy “DynoWiper,” a new destructive malware variant, against Polish energy infrastructure. The attack was contained before causing outages, but the technical sophistication marks an evolution from their 2015-2016 Ukraine grid attacks.
Key findings:
DynoWiper specifically targets Schneider Electric SCADA systems. Uses legitimate OT protocols (Modbus, IEC 61850) to blend with normal traffic. Includes anti-forensics modules that corrupt PLC firmware after wiping. Pre-positioned for months before activation.
The timing isn’t coincidental. Poland’s critical role in NATO logistics and Ukraine support makes it a high-priority target. This operation signals preparation for potential escalation.
This marks the first known Sandworm attack targeting a NATO member’s critical infrastructure. That detail matters.
OT/ICS operators: Baseline legitimate OT traffic patterns now. Detection rules for anomalous Modbus commands should be deployed across all energy sector SCADA environments.
Source: Dragos Threat Intelligence, CERT Polska, January 2026
5. When Hacktivists Cause Physical Impact
CISA Alert AA25-343A: The line between digital and physical has dissolved.
In January, CISA issued a rare alert documenting pro-Russia hacktivist groups achieving physical impact on US critical infrastructure. Water treatment facilities experienced pump failures. Manufacturing PLCs entered unsafe states.
What changed:
Hacktivist groups are now sharing ICS exploitation guides on Telegram. Operational technology defaults (default passwords, exposed HMIs) create attack surface. Groups previously limited to DDoS and defacement have upskilled to OT compromise.
The attacks weren’t sophisticated. They didn’t need to be. Internet-exposed HMIs with default credentials were the only requirement.
Critical infrastructure operators have known about these exposures for years. Regulators have issued guidance. Hacktivists have now become the enforcement mechanism.
Action required: Internet-exposed ICS asset discovery should be a weekly automated scan. Default credential campaigns need executive sponsorship and deadlines.
Source: CISA Advisory AA25-343A, January 2026
6. OAuth: The Supply Chain You Forgot to Secure
Two SaaS supply chain compromises expose the trust problem in enterprise OAuth.
January saw back-to-back OAuth-based supply chain attacks targeting enterprise SaaS platforms:
Salesloft-Drift Compromise: Attacker compromised Drift’s OAuth integration with Salesloft. All customers with the integration active had mailbox access exposed. Estimated 4,200 organizations affected.
Gainsight Customer Data Exfiltration: OAuth token theft from Gainsight’s customer success platform. Product usage data for 800+ enterprise customers exfiltrated. Competitive intelligence implications significant.
The pattern: OAuth tokens are persistent, broadly scoped, and rarely audited. Once compromised, they provide silent access until explicitly revoked.
OAuth security priorities:
Inventory all OAuth grants across your SaaS portfolio. Implement just-in-time access for sensitive integrations. Monitor for OAuth grants from unusual locations or devices. Establish a periodic OAuth grant review process.
Source: Obsidian Security, January 2026
Quick Hit: Scattered Spider Joins DragonForce
The social engineering experts have a new home.
Following the disruption of their infrastructure in late 2025, Scattered Spider operators have affiliated with the DragonForce ransomware cartel. This partnership combines Scattered Spider’s elite social engineering capabilities with DragonForce’s infrastructure and ransom negotiation experience.
Expect SIM swapping and help desk social engineering attacks to increase through Q1 2026, now backed by more robust ransomware deployment.
Source: Mandiant M-Trends, January 2026
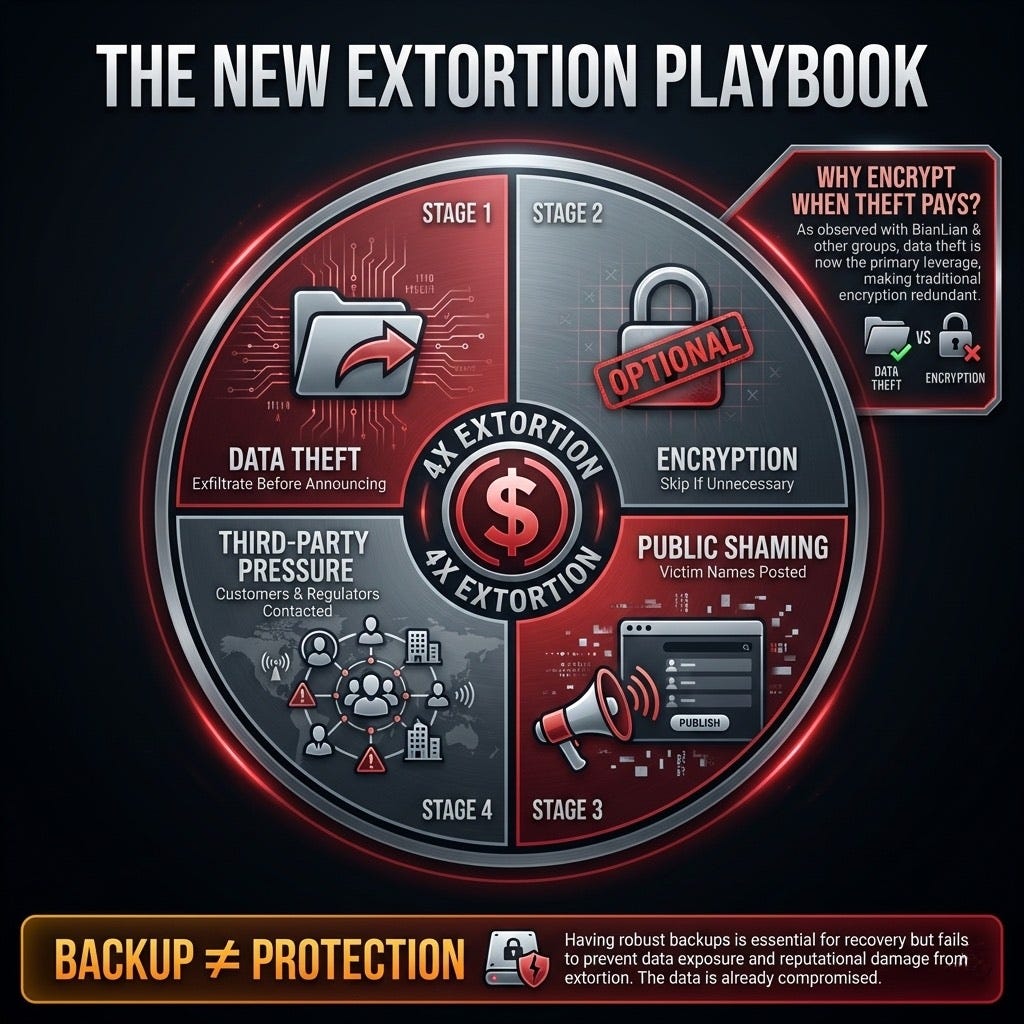
Trend Watch: Encryption Is Optional
Quadruple extortion becomes the new baseline.
January data confirms a shift in ransomware economics: encryption is increasingly optional. The modern extortion playbook:
Data theft: Exfiltrate before announcing presence
Encryption: Sometimes deployed, sometimes skipped
Public shaming: Victim names posted to leak sites
Third-party notification: Customers, regulators, and partners contacted directly
Groups like BianLian have abandoned encryption entirely. Why invest in complex crypto when data theft alone generates payments?
Defensive implication: Data Loss Prevention (DLP) and exfiltration detection are now as critical as backup integrity.
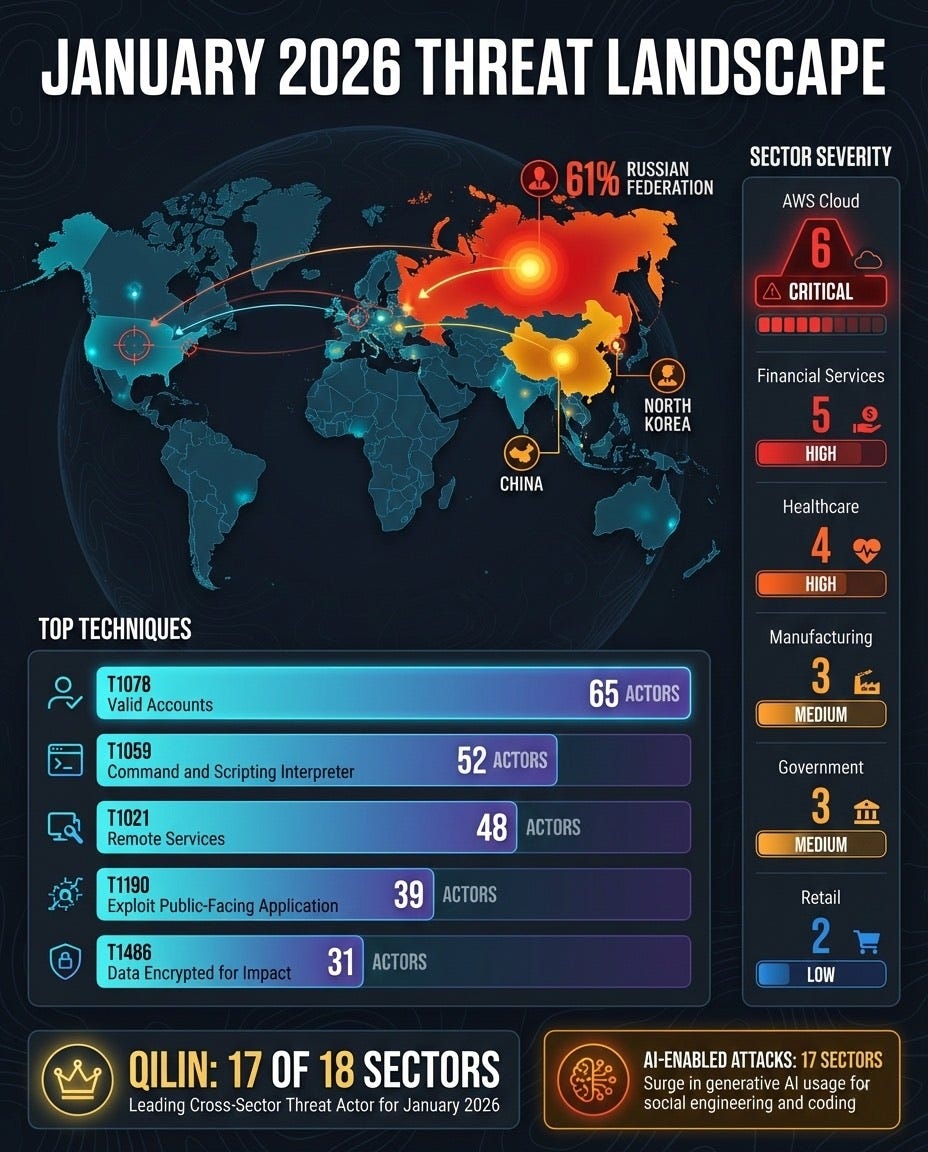
January 2026 By The Numbers
Qilin led all actors, active in 17 of 18 sectors analyzed
T1078 (Valid Accounts) was the #1 technique, used by 65 actors across all sectors
Russia accounted for 61% of attributed actor activity
AI-enabled attacks flagged as emerging signal in 17 sectors
Custom Sector - Amazon AWS Cloud Technologies sector had highest severity concentration (6 CRITICAL)
Defensive Playbook: February Priorities
Given the wide spread of attack vectors this month, here are some defensive measures that you can take to protect your organization over the next 90+ days.
NOTE: Every environment is different, and Intruvent has not examined your environment. These are general recommendations that you should undertake only after evaluating their usefulness and efficacy for your specific circumstances.
Immediate (This Week)
Audit S3 bucket SSE-C permissions and access patterns
Review OAuth grants for all SaaS integrations
Scan for internet-exposed ICS/OT assets
Short-Term (30 Days)
Deploy CloudTrail alerting for unusual S3 encryption operations
Implement automated response for OAuth-based compromise indicators
Baseline OT network traffic for anomaly detection
Strategic (90 Days)
Evaluate data exfiltration detection capabilities vs. encryption-focused controls
Develop 8-minute response playbook for cloud credential compromise
Third-party OAuth integration security review program
Sources
Intruvent BRACE Sector Reports - Cross-Sector Threat Intelligence, January 2026
Halcyon Research - Codefinger SSE-C Analysis, January 2026
Wiz Cloud Threat Intelligence - AI-Accelerated Breach Study, January 2026
Chainalysis - Bybit Incident Analysis, January 2026
FBI IC3 - North Korea Cryptocurrency Advisory, January 2026
Dragos Threat Intelligence - DynoWiper Technical Report, January 2026
CERT Polska - Energy Sector Incident Report, January 2026
CISA - Advisory AA25-343A, January 2026
Obsidian Security - OAuth Supply Chain Report, January 2026
Mandiant M-Trends - RaaS Evolution Update, January 2026
INTRUVENT EDGE is published monthly. For the complete cross-sector technical analysis, see the January 2026 Cross-Sector Trends Report.
Questions? Feedback? Reply to this email or reach out at contact@intruvent.com