Intruvent EDGE: Inside INC Ransomware's Ruthless Playbook
How a cybercriminal startup became one of healthcare's most persistent predators
In March 2024, Julie White, chief executive of NHS Dumfries and Galloway in Scotland, called it an “utterly abhorrent criminal act.”
She wasn’t being dramatic.
Cybercriminals had quietly copied 3 terabytes of patient data from her organization’s servers. Genetic reports. Letters between doctors. Psychological evaluations. Records affecting up to 150,000 people. And they were threatening to publish everything unless the NHS paid up.
The group called themselves INC Ransom. Within eight months, they would hit Alder Hey Children’s Hospital in Liverpool, one of Europe’s largest pediatric facilities. Same playbook. Same ruthlessness. Sophisticated attacks by skilled attackers.
[Editor's Note] If you work in cybersecurity at a children's hospital, or know someone who does, please reach out (contact@intruvent.com). Intruvent provides free threat intelligence to children's hospitals worldwide. You all have a hard enough job already. Thank you for all that you do!
Welcome to INC Ransomware, an operation that has positioned itself as one of the most prolific groups in the ransomware ecosystem. Defenders and Threat Hunters, we have FREE Intel Guides available, please see the links below.
The Origin Story
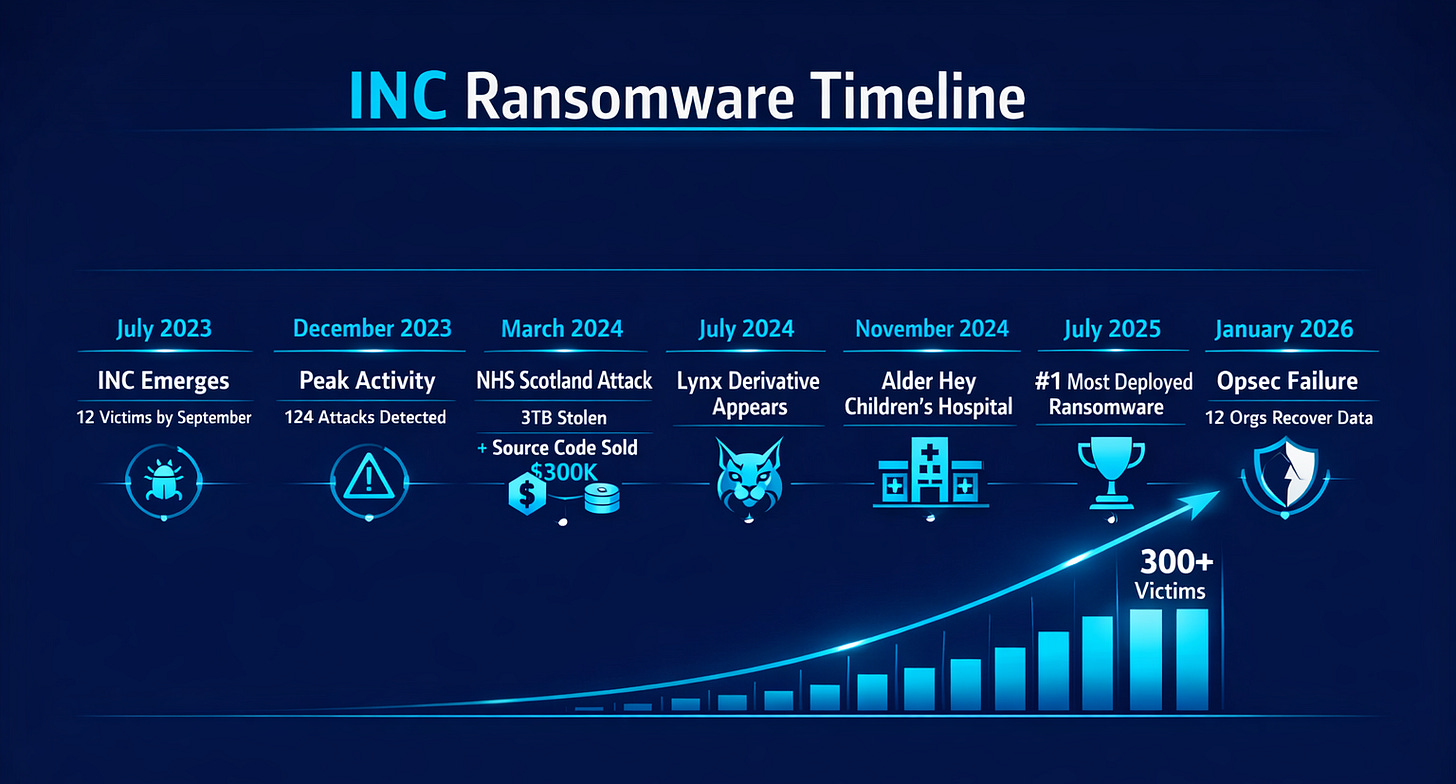
INC appeared in July 2023, seemingly from nowhere. Unlike most ransomware groups that splinter from existing operations, INC showed up as an original creation. Secureworks tracks them as GOLD IONIC. MITRE cataloged them as G1032. By September 2023, just two months in, they had posted 12 victims to their dark web leak site.
What set INC apart was their messaging. They framed intrusions as unauthorized security audits. “We’re making your environment more secure” was the implicit pitch. It’s manipulation dressed up as customer service.
The numbers tell the story: 162 victims in 2024. Over 300 in 2025. In July 2025, INC became the most deployed ransomware by victim count. They average 11 organizations per month.
How INC Gets In
The trail often starts with internet-facing systems.
CVE-2023-3519 (Remote Code Execution) in Citrix NetScaler stands out as a consistent favorite. This vulnerability allows attackers to execute code without authentication. CISA issued an advisory in July 2023. INC was exploiting it almost immediately.
INC affiliates have also exploited Fortinet products, including FortiClient EMS (CVE-2023-48788) and FortiOS (FG-IR-24-535). In one documented case, attackers created new SSL VPN configurations on a compromised FortiGate to maintain persistent access.
But the scariest entry point might be the most mundane. Microsoft tracks an affiliate called Vanilla Tempest (formerly Vice Society) that adopted INC ransomware for healthcare targeting. Their approach? SEO poisoning. They manipulate search results so that when employees search for common business documents, they land on malicious sites that deploy Gootloader malware. No vulnerability required. Just someone searching for a contract template.
Once inside, real people poke around the network. They run reconnaissance with netscan.exe and AdFind. They harvest credentials using tools like lsassy.py and Impacket’s secretsdump. In one case documented by HvS-Consulting, INC operators performed Kerberoasting and cracked the Domain Admin password within 48 hours of initial access.
Double Extortion
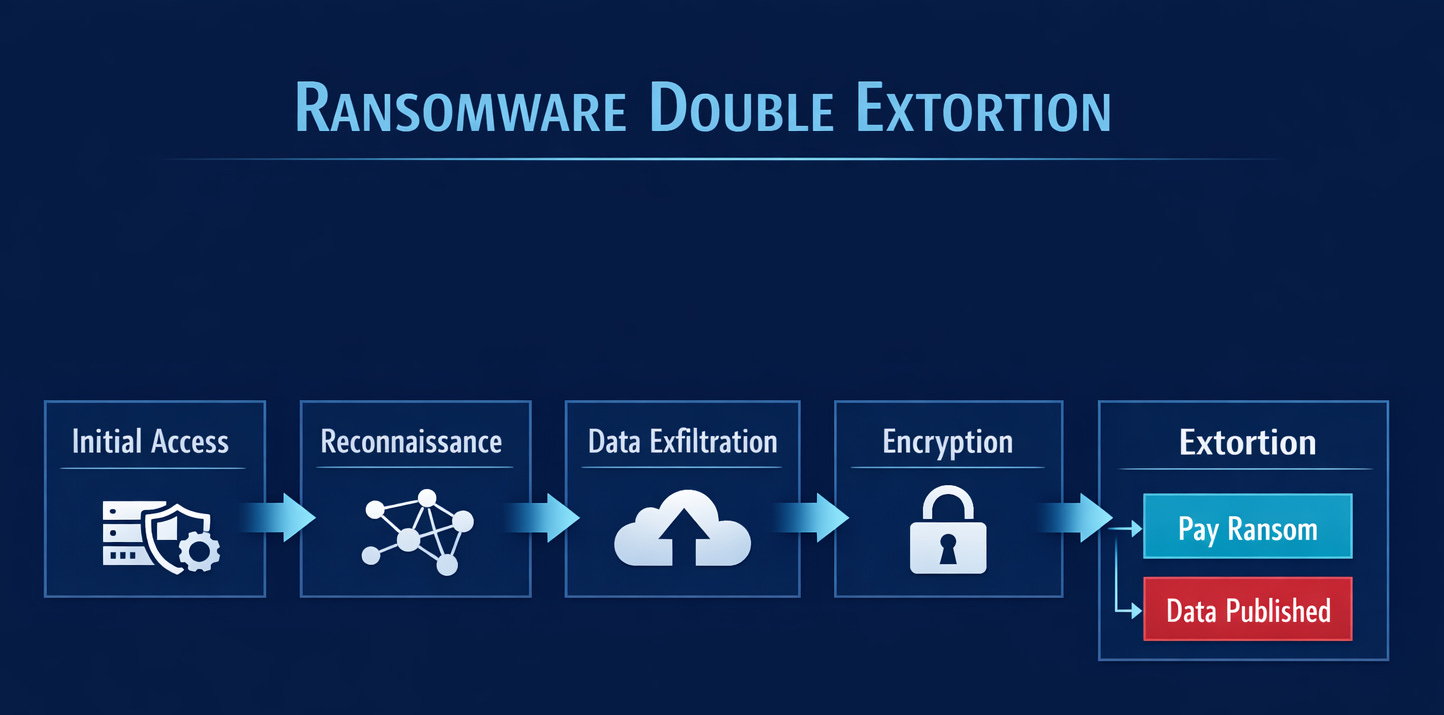
By the time encryption begins, attackers have typically spent days inside the network. They’ve exfiltrated terabytes using MEGASync, Rclone, or Restic. They’ve mapped backup systems.
Then files get the “.INC” extension. Ransom notes appear everywhere. Sometimes the ransomware sends notes to network printers, ensuring everyone in the building knows what’s happening.
INC operates two leak sites: a private one for negotiations, and a public one for dumping data from organizations that refuse to pay. The demands are calibrated. Attackers review financial records and cyber insurance policies to set their price. You pay one sum to unlock your files, you pay another sum to ensure they don’t leak your files.
Some attacks skip encryption entirely. ReliaQuest documented cases where INC affiliates exfiltrated data but never deployed the encryptor. Pure extortion, no encryption required.
Healthcare in the Crosshairs
Healthcare accounted for 29% of INC’s attacks in early 2025. Sophos identified INC as one of the three most prominent ransomware groups targeting healthcare organizations last year.
Beyond the NHS attacks, the victim list reads like a healthcare industry directory. Compass Health Network, a mental health provider, lost 500,000 sensitive records including therapy notes and psychiatric diagnoses. OnePoint Patient Care, a hospice pharmacy provider, had a breach affecting 1.74 million individuals.
The UK’s NHS has a policy of not paying ransoms. INC knows this. They keep targeting British healthcare anyway.
The implication: INC isn’t targeting healthcare solely because these organizations might pay. Medical records have long shelf lives on criminal marketplaces. They enable identity theft and fraud for years after the initial breach.
The Code That Wouldn’t Die
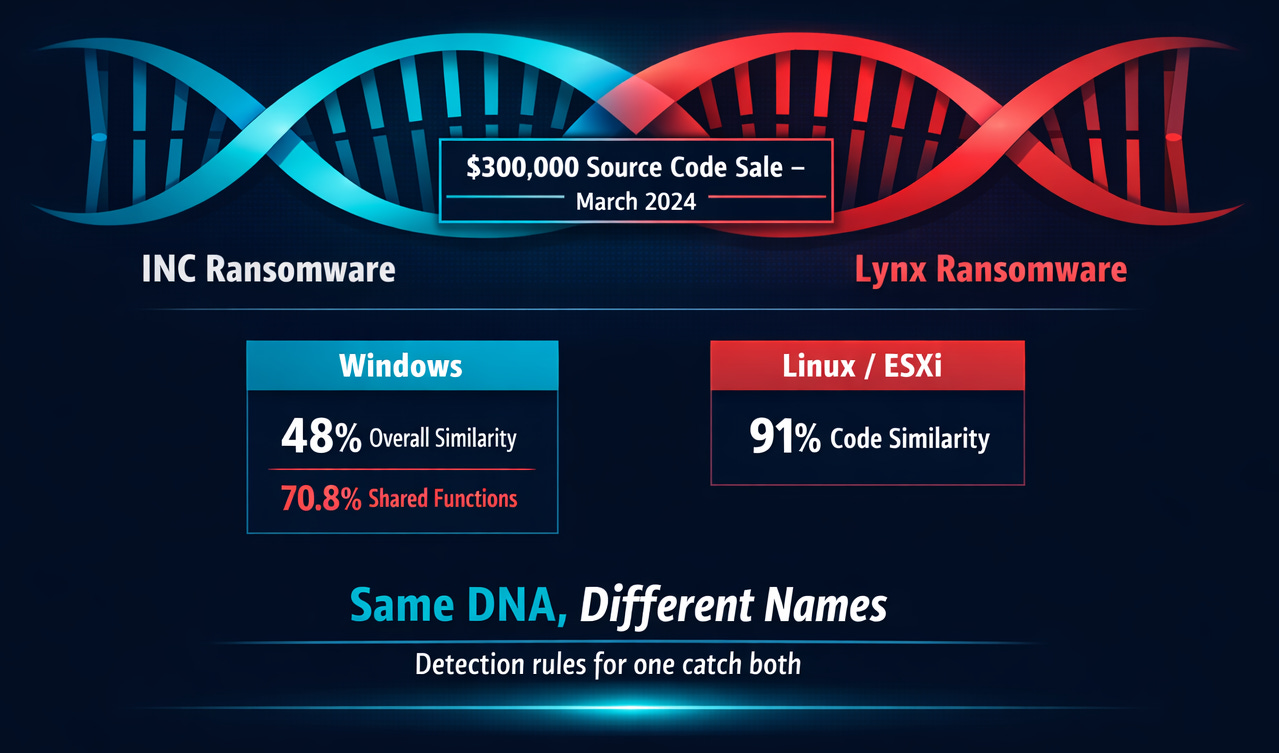
In March 2024, someone using the handle “salfetka” appeared on Russian-language forums selling INC’s complete source code for $300,000, limited to three buyers.
By July 2024, a new operation called Lynx emerged. Binary analysis showed 48% overall code similarity with INC. The Linux variants showed 91% overlap.
But here’s the twist: INC didn’t go away. Both operations continue claiming victims in parallel. Some incident responders have seen Lynx ransomware deployed in attacks later claimed on INC’s leak site. For defenders, detection rules for one catch both.
And then came the opsec failure. In January 2026, security researchers discovered that INC operators had reused Restic backup infrastructure across multiple intrusions without properly securing it. The mistake allowed data recovery for 12 US organizations.
Even cybercriminals make configuration errors.
Beyond Healthcare
While healthcare dominates the victim list, INC’s appetite extends further.
Stark Aerospace, a US missile systems and aerial weapons manufacturer, had 4TB of data claimed stolen. The attackers allegedly accessed source code, design plans, employee passports, and UAV firmware.
OnSolve, the company behind the CodeRED emergency alert system used by municipalities nationwide, was hit in November 2025. The attackers demanded $950,000 and exfiltrated customer data including plaintext passwords. The breach forced decommissioning of legacy infrastructure that affected emergency communication capabilities across the country.
Critical infrastructure. Defense contractors. Emergency services. INC doesn’t have any off-limit sectors.
Detection Quick Reference
See our full guides for more info, but here is a cheat sheet for you on quick detection items.
Pre-encryption warning signs:
AnyDesk, ScreenConnect, or TightVNC on servers where they don’t belong
netscan.exe or AdFind.exe execution
MEGASync, Rclone, or Restic on non-backup systems
Shadow copy deletion commands
Ransomware execution indicators:
Files with
.INCextensionINC-README.TXTorINC-README.HTMLin directoriesINC_Updatescheduled task
Patch priority:
Citrix NetScaler: CVE-2023-3519, CVE-2023-4966
Fortinet: CVE-2023-48788, FG-IR-24-535
Full guides are available for FREE on the Intruvent site:
What This Means For You
INC represents exactly the threat mid-market enterprises and healthcare organizations need to plan for: sophisticated enough to bypass basic defenses, patient enough to conduct proper reconnaissance, ruthless enough to publish your data regardless of harm.
[IMPORTANT] Patch perimeter devices. Citrix NetScaler, FortiClient EMS, and FortiOS have all featured in INC intrusions. Verify your patch status today.
Monitor living-off-the-land techniques. INC operators use PsExec, WMI, and legitimate remote tools. Behavioral detection catches what signatures miss.
Watch for unauthorized RMM tools. AnyDesk, ScreenConnect, and TightVNC on servers where they don’t belong is a red flag.
Assume breach in your backup strategy. INC operators study networks before encryption. Air-gapped or immutable backups provide the recovery option they work hardest to eliminate.
The Uncomfortable Truth
INC has operated continuously for over two and a half years. They sold their source code and kept going. They spawned Lynx, adding hundreds more victims. They made an opsec mistake that cost them leverage over a dozen organizations, and they’re still running.
The 150,000 people in Scotland whose medical records ended up on the dark web didn’t choose to become part of this story. Neither did the patients at Alder Hey or the communities relying on CodeRED for emergency alerts.
Understanding how groups like INC operate won’t prevent every attack. But it helps organizations focus limited security resources where they matter most.
That’s the work. One intrusion at a time.
Thanks for reading Intruvent Edge!
Research Sources: Secureworks CTU, Palo Alto Unit 42, Trend Micro, MOXFIVE, Microsoft Threat Intelligence, Check Point Research, Sophos X-Ops, HvS-Consulting, ReliaQuest, Huntress, CISA
Last Updated: February 2026