Intruvent EDGE: CISA Confirms Iranian Disruption of US Critical Infrastructure
From default passwords to legitimate engineering tools: CyberAv3ngers have leveled-up their capabilities, and what Rockwell shops should do this week.
What Happened
On April 7, 2026, six federal agencies published joint advisory AA26-097A with two phrases that should concern every critical infrastructure operator in America: “operational disruption” and “financial loss.”
The advisory, signed by the FBI, CISA, NSA, EPA, Department of Energy, and US Cyber Command, confirms that Iranian-affiliated cyber actors have actively disrupted programmable logic controllers across US water and wastewater systems, energy facilities, and government installations. Not “attempted to access.” Not “may have compromised.” Disrupted. With confirmed operational and financial impact.
The threat actor is CyberAv3ngers, a persona operated by Iran’s Islamic Revolutionary Guard Corps Cyber-Electronic Command (IRGC-CEC). The same group that compromised water utility PLCs in Pennsylvania in November 2023. The same group whose six operators were designated by the US Treasury in February 2024. The same group the State Department has offered a $10 million bounty on.
They have advanced their tradecraft. Where earlier operations relied on internet-exposed devices with default credentials, they are now targeting Rockwell Automation controllers, the most widely deployed industrial automation platform in North America, using legitimate Rockwell engineering software to establish connections that read as normal operator activity on most network sensors.
If your organization operates Rockwell CompactLogix or Micro850 PLCs, particularly in water, energy, or government sectors, this advisory is about you.
From Public Defacement to Legitimate Tooling: The CyberAv3ngers Evolution
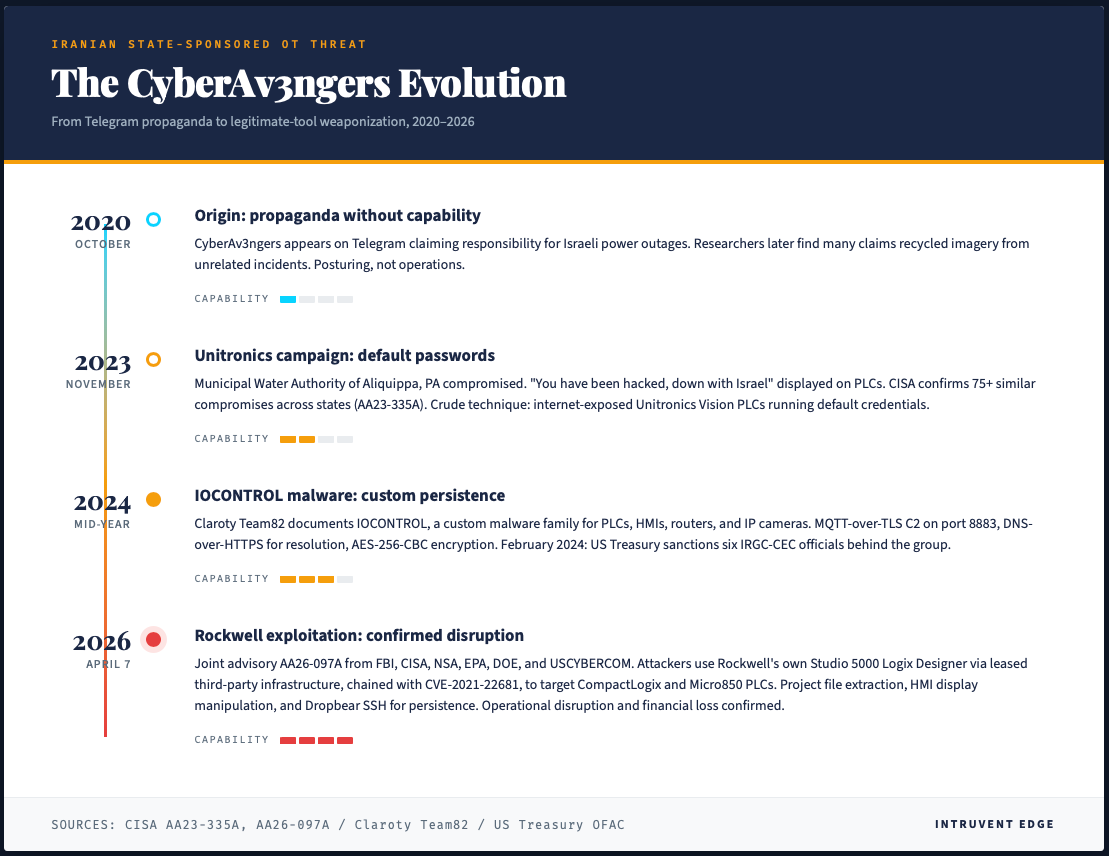
CyberAv3ngers first surfaced in October 2020 on Telegram, claiming responsibility for power outages in Israel. The group’s early public activity emphasized messaging, and some claims were later correlated to imagery from separate incidents. Those years established the brand. The years that followed established the capability.
In November 2023, the Municipal Water Authority of Aliquippa, Pennsylvania discovered that their Unitronics Vision Series PLC had been compromised and was displaying a defacement message. CISA confirmed the attack and published advisory AA23-335A. The operators took a pragmatic technical approach, exploiting internet-exposed PLCs running default credentials. Within weeks, CISA documented at least 75 similar compromises across multiple states. The target selection was deliberate: a specific vendor, in a specific sector, at a scale that demonstrated operational tempo.
The 2023 campaign confirmed CyberAv3ngers as a capable operational group with sustained interest in US critical infrastructure. The 2026 campaign shows where that capability has grown.
According to AA26-097A, the operators are now using “leased, third-party hosted infrastructure with configuration software, such as Rockwell Automation’s Studio 5000 Logix Designer software, to create an accepted connection to the victim’s PLC.” They are not exploiting a software vulnerability in the traditional sense. They are using the exact tools that legitimate engineers use to program and maintain these controllers, which means the resulting network traffic looks like engineering activity to most detection tooling.
This is a meaningful escalation in capability. Studio 5000 Logix Designer is Rockwell’s professional engineering environment. Using it requires stolen credentials, a compromised engineering workstation, or exploitation of CVE-2021-22681, a cryptographic key vulnerability that permits an actor who obtains a specific key to authenticate to affected PLCs without valid credentials. CISA added CVE-2021-22681 to its Known Exploited Vulnerabilities catalog in March 2026, confirming active exploitation.
The target set has expanded in proportion to the capability. Rockwell Automation dominates the North American industrial automation market. CompactLogix and ControlLogix controllers run water treatment plants, power generation facilities, manufacturing lines, and oil and gas operations across the continent. Censys identified 5,219 internet-exposed hosts globally responding to EtherNet/IP protocols and identifying as Rockwell Automation devices. 74.6% of them, approximately 3,890 devices, are in the United States.
Inside the Attack Chain
The AA26-097A advisory describes a multi-phase operation targeting specific ports on exposed Rockwell controllers:
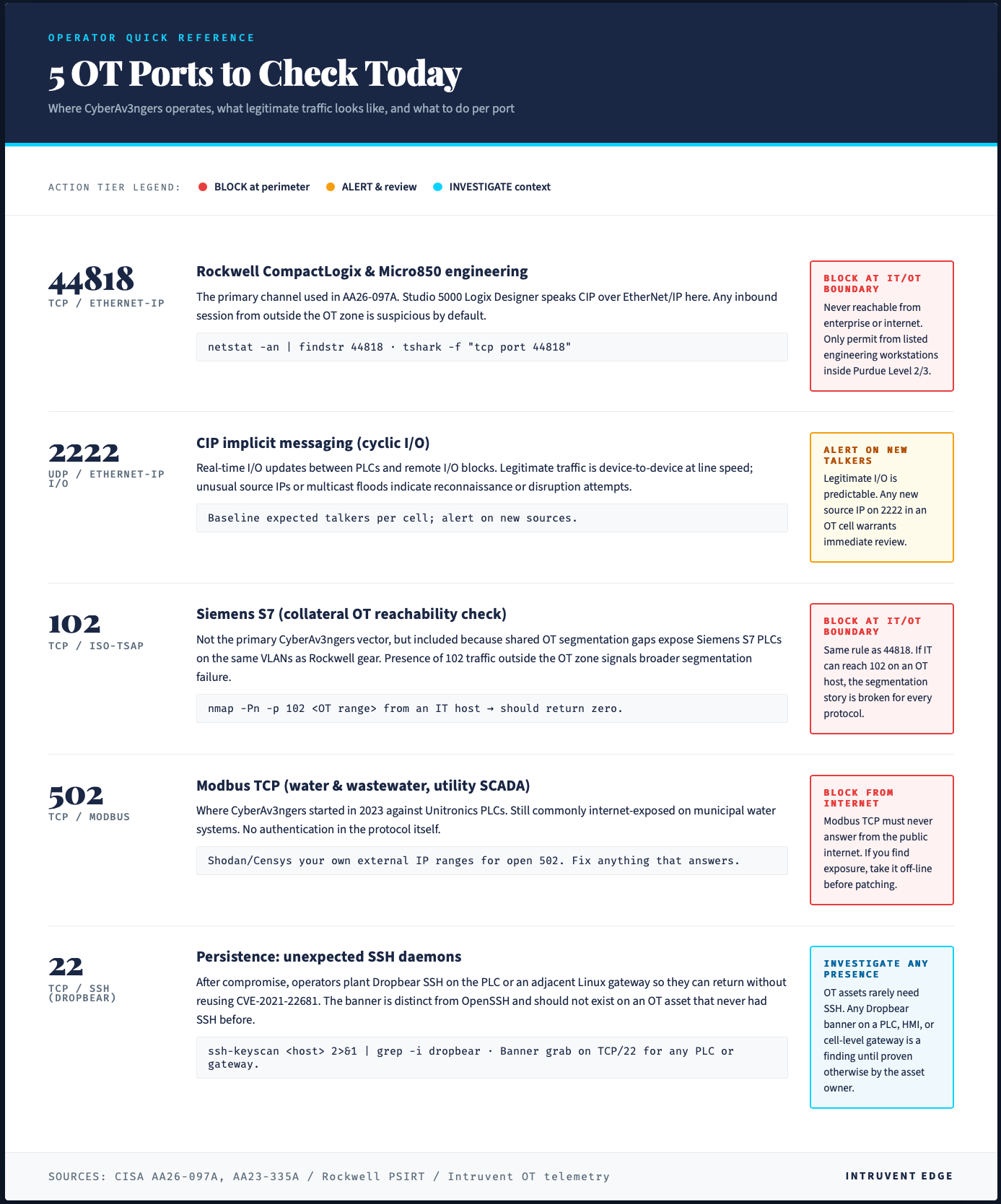
Port 44818 (EtherNet/IP): The primary Rockwell Automation industrial protocol. This is how Studio 5000 communicates with CompactLogix and other Logix-family controllers.
Port 2222: Used for OT configuration and some Rockwell-specific services.
Port 102 (ISO-TSAP): The Siemens S7 communication protocol. Its presence in the advisory suggests the operators are scanning for multiple PLC vendors in parallel.
Port 502 (Modbus TCP): A legacy industrial protocol still widely used. Many Rockwell controllers support Modbus for integration with third-party systems.
Port 22 (SSH): Indicates deployment of persistent access mechanisms. Picus Security’s analysis of the campaign notes that “attackers deployed Dropbear SSH on victim endpoints, providing persistent remote access surviving PLC reboots.”
Once connected, the operators performed two categories of post-access activity:
Project file extraction. PLC project files (with .ACD extension in Rockwell environments) contain the ladder logic, control sequences, and configuration parameters that define how the controller operates. Extracting these files yields a complete blueprint of the target facility’s automation logic, useful for reconnaissance, follow-on operations, or potential kinetic effects.
HMI/SCADA display manipulation. The operators modified data displayed on human-machine interfaces and SCADA systems. This is particularly consequential in critical infrastructure environments. If operators cannot trust what their screens tell them, they cannot safely run the facility. A manipulated display could show normal pressure readings while a tank overflows, or hide a dangerous temperature rise until equipment fails.
The advisory confirms that “some of the victims experienced operational disruption and financial loss.” The FBI declined to provide additional details about specific incidents.
Who Is CyberAv3ngers?
CyberAv3ngers is a state-sponsored program run by the IRGC-CEC, the cyber-electronic warfare arm of Iran’s Islamic Revolutionary Guard Corps. It is a well-resourced group with sustained access to infrastructure, tooling, and personnel, operating within an established national cyber program.
The US Treasury designated six IRGC-CEC officials in February 2024 for their roles in the group. The State Department has offered a $10 million reward for information leading to the identification or location of any person who, while acting at the direction of a foreign government, participates in malicious cyber activities against US critical infrastructure.
The group is tracked under multiple names across the vendor community:
Storm-0784 (Microsoft)
Bauxite (Dragos)
UNC5691 (Mandiant)
G1027 (MITRE ATT&CK)
In January 2026, the group rebranded its Telegram channel from “CyberAv3ngers” to “Cyber4vengers.” The rebrand coincided with a shift toward more technically mature operations.
Leaked records from December 2025 confirmed operational connections between CyberAv3ngers and Moses Staff, another Iranian state-sponsored group known for destructive wiper operations. Check Point Research has documented approximately 60 affiliated pro-Iranian groups that adopt CyberAv3ngers techniques.
The IOCONTROL Connection
The Rockwell campaign is not the only active CyberAv3ngers toolset. A parallel thread in the group’s capability development was documented two years earlier.
In mid-2024, Claroty’s Team82 published analysis of a custom malware family called IOCONTROL, attributed to CyberAv3ngers. IOCONTROL is designed to run on a variety of IoT and OT devices, including PLCs, HMIs, routers, and IP cameras. The malware uses:
MQTT over TLS on port 8883 for command and control
DNS-over-HTTPS to resolve C2 infrastructure, evading traditional DNS monitoring
AES-256-CBC encryption for all communications
IOCONTROL marked a clear step beyond the 2023 Unitronics operations. Where the earlier work centered on public-facing defacement, IOCONTROL extended the toolkit to persistent access and programmatic manipulation of industrial processes across a broader range of device types. By 2024, the group was already investing in purpose-built OT malware, a year and a half before the Rockwell activity in AA26-097A surfaced publicly.
The relationship between the IOCONTROL work and the 2026 Rockwell exploitation is not explicitly stated in public reporting. Both lines of operation target overlapping sectors and reflect a consistent trajectory toward persistent, vendor-agnostic access to industrial control environments.
Why This Advisory Is Different
CISA has published many advisories about threats to critical infrastructure. Most describe potential risks or document intrusion attempts. AA26-097A is different because it confirms actual impact.
On March 18, 2026, the CISA Acting Director stated that CISA was operating at “steady state” regarding Iranian cyber threats, despite the ongoing military conflict between the US, Israel, and Iran. The implication at the time was that threat activity remained within normal parameters.
AA26-097A, published 20 days later, functionally updates that assessment. The advisory confirms that Iranian actors have not merely attempted to access critical infrastructure; they have disrupted it. Facilities have experienced operational impacts. Organizations have incurred financial losses.
This is also the first joint advisory of the current conflict signed by six federal agencies, including US Cyber Command’s Cyber National Mission Force. The breadth of signatories signals the severity of the threat and the confidence level in the attribution.
The geopolitical context matters. Since Operation Epic Fury began on February 28, 2026, the US and Israel have conducted sustained military operations against Iran. The Strait of Hormuz has been effectively closed for over a month. Iran’s Supreme Leader was killed in an early strike. This week, President Trump issued an ultimatum threatening to destroy “every bridge” and “every power plant in Iran” if the Strait is not reopened.
CyberAv3ngers is one of Iran’s primary instruments of asymmetric cyber operations. The confirmed disruptions in AA26-097A indicate that instrument is in active use against American infrastructure.
What You Should Do
A Note Before You Act
The guidance below describes general defensive practices for OT and ICS environments. It is not prescriptive direction for your specific network.
Operational technology environments are safety-critical. Taking a PLC offline, altering network segmentation, disabling services, or changing keyswitch positions can produce consequences that extend well beyond IT, including process upsets, equipment damage, safety incidents, and regulatory exposure.
Before implementing any step in this section:
Review the guidance with your OT engineering team, facility operators, and safety personnel.
Verify compatibility with your specific device models, firmware versions, and operational context.
Consult vendor documentation, including Rockwell Automation advisories, for device-specific procedures.
Coordinate changes through your organization’s change-management and outage-planning processes.
Where doubt exists, engage a qualified OT cybersecurity professional familiar with your environment.
This newsletter is threat intelligence reporting, not engineering direction. Intruvent Technologies provides this information on an “as is” basis, without warranties of any kind, and accepts no liability for any operational, safety, financial, or other consequences arising from actions taken on the basis of this content. Decisions about your systems are yours to make, with your team, based on your knowledge of your environment.
Right Away
Take internet-exposed PLCs offline. There is no legitimate reason for a PLC to be directly accessible from the public internet. Every Rockwell CompactLogix, Micro850, or similar controller that responds to public internet queries is a potential target. If your organization has exposed devices, disconnect them now. Remote access should be routed through secured gateways, jump servers, or VPNs with multi-factor authentication.
Check the ports. Scan your external perimeter for services on TCP 44818 (EtherNet/IP), 2222, 102 (ISO-TSAP), 502 (Modbus), and 22 (SSH). Any inbound access to these ports from untrusted networks should be blocked.
Set physical mode switches to RUN. CompactLogix controllers have a physical keyswitch that can be set to RUN mode, preventing remote programming changes. This is a simple, effective control that many operators overlook. An actor who gains network access to a controller in RUN mode cannot upload new logic without physical access to the device.
Audit for Dropbear SSH. The advisory indicates operators deployed Dropbear SSH for persistence. Dropbear is a lightweight SSH server that does not belong on most PLCs. Search for unexpected SSH services on your OT devices.
This week
Patch CVE-2021-22681. This cryptographic key vulnerability affects Rockwell Studio 5000 Logix Designer and enables authentication bypass. Rockwell has released mitigations, check them out.
Review your cellular connectivity. Many PLCs in remote locations use cellular modems for remote access. These connections often bypass corporate firewalls and security controls. Audit which devices have cellular connectivity and whether that connectivity is necessary.
Enable network monitoring at OT boundaries. If you do not have visibility into traffic entering and leaving your OT networks, you cannot detect this activity. Deploy network detection and response capabilities that understand industrial protocols like EtherNet/IP and Modbus.
Going forward
Implement network segmentation. PLCs should sit on isolated network segments with controlled access points. Traffic between IT and OT networks should flow through monitored chokepoints. “Air gaps” that exist only on network diagrams provide no protection.
Disable unnecessary services. VNC, Telnet, FTP, and HTTP management interfaces on PLCs provide additional attack surface. Disable anything not required for operation.
Monitor for configuration changes. Establish baselines for PLC project files and alert on unexpected modifications. A change to ladder logic should trigger immediate investigation.
Develop offline recovery procedures. If your PLCs are compromised, can you restore them from known-good backups? Are those backups stored offline where they cannot be modified by the same actor? Test your ability to rebuild a compromised controller from scratch.
Indicators of Compromise
The CISA advisory includes a STIX file with machine-readable indicators at https://www.cisa.gov/sites/default/files/2026-04/AA26-097A.stix_.xml.
Target ports:
TCP 44818 (EtherNet/IP)
TCP 2222 (OT configuration)
TCP 102 (ISO-TSAP)
TCP 502 (Modbus)
TCP 22 (SSH)
Affected devices:
Rockwell Automation CompactLogix
Rockwell Automation Micro850
Any Rockwell/Allen-Bradley device on EtherNet/IP
CVE:
CVE-2021-22681 (CVSS 9.8): Authentication bypass via insufficiently protected cryptographic key in Studio 5000 Logix Designer
Behavioral indicators:
Studio 5000 connections from non-engineering workstations
Dropbear SSH processes on PLC or HMI devices
Modified PLC project files (.ACD)
Inconsistencies between SCADA displays and physical process values
Outbound connections from OT devices to unexpected IP ranges
Sources
CISA Advisory AA26-097A, April 7, 2026
The Register: Iran Intruders Disrupting US Water, Energy Facilities
CISA Advisory AA23-335A, November 2023 Unitronics Campaign
More Iran Cyber Threat Intelligence
The CyberAv3ngers campaign is part of a broader pattern of Iranian cyber operations escalating alongside the ongoing military conflict. We’re tracking 16+ Iranian threat groups actively targeting US and allied infrastructure.
For continuously updated threat actor profiles, IOC feeds, detection rules, and geopolitical context on the Iran cyber threat, visit the Intruvent Iran Cyber Threat Intelligence Center.
Resources include:
CyberAv3ngers, Handala, MuddyWater, and 13+ other Iranian APT profiles
Iran Conflict SITREP (updated bi-weekly)
OT/ICS-specific detection queries for Splunk and Microsoft Sentinel
Indicators of compromise with blocking guidance
Intruvent Edge is a bi-weekly threat intelligence newsletter from Intruvent Technologies. For monthly threat reporting and detection, visit intruvent.com/brace.